Key Takeaways:
- Siloed Teams Are Your Hidden Multi-Cloud Cost: Federal and state agencies gain flexibility with multi-cloud adoption, but fragmented CloudOps, security, and compliance teams create duplicated effort, delayed authorizations, and governance bottlenecks that quietly compound across every stage of the cloud lifecycle.
- Multi-Cloud Environments Increase Complexity: Each cloud provider doesn't simply introduce another platform; it expands the attack surface and requires updates to security controls, ATO packages, and monitoring strategies. In multi-cloud environments, managing separate control models, compliance requirements, and governance processes transforms manageable complexity into exponential friction.
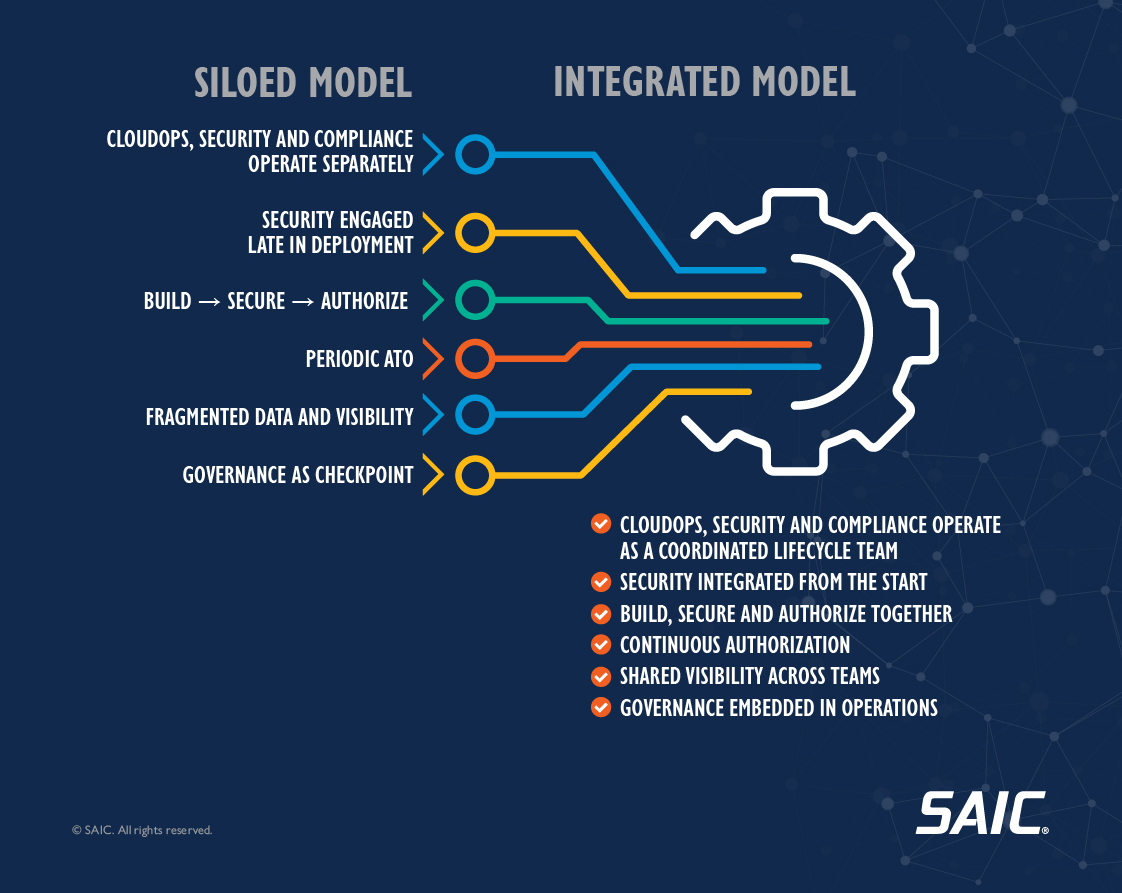
- Integration Is the Path Forward—and Already Underway: The better approach treats CloudOps, security, and compliance as an integrated system where security is built into design from the start, authorization is continuous, and all functions share visibility and data. Agencies across the federal and state landscape are already making this practical shift to a mission-centered model.
Operating across multiple cloud service providers gives federal and state agencies greater flexibility, resilience, and access to best-of-breed tools for their missions. But adopting multi-cloud is not the same as operating it well, and the gap between the two is where agencies often encounter significant friction.
Today’s systems must be designed to reduce risk from the start and adapt as conditions change. That requirement has exposed a structural problem: Cloud Operations (CloudOps) teams build and manage cloud services. Security teams implement and monitor controls to protect them. Compliance and Authority to Operate (ATO) teams assess whether those controls meet policy requirements and formally authorize the system to operate. But rather than working as an integrated team, they function as three independent workstreams.
This misalignment compounds quietly across every stage of the cloud lifecycle, leading to duplicated effort, delayed ATO decisions, rework triggered by late-stage risk findings, inconsistent financial management actions and timing, and governance structures that slow decisions instead of enabling them.
Multi-Cloud Multiplies the Coordination Burden
Every new cloud service provider an agency adopts introduces more than another platform to manage. It expands the attack surface and materially changes the underlying security architecture.
That shift requires updates to security control implementations, revisions to the ATO package and adjustments to the continuous monitoring strategy. Meanwhile, each cloud service provider brings its own control models, compliance requirements, operational tooling, and governance processes. Even when providers align to federal frameworks, control inheritance and implementation can differ in meaningful ways.
In a single-cloud environment, complexity is manageable. In multi-cloud, however, complexity does not simply increase; it multiplies.
How Siloed Operations Look in Practice
As they adopt multi-cloud, agencies across the federal and state landscape are navigating a common set of challenges that stem directly from this fragmented operating model.
Security engaged late in the lifecycle.
In many organizations, cybersecurity still operates independently from cloud architecture and DevSecOps pipelines. Security reviews often occur after key deployment decisions have already been made. Findings surface late, triggering rework, delays, and inconsistent enforcement of security baselines. Instead of shaping architecture from the outset, security becomes a corrective function.
ATO processes built for static systems.
Traditional ATO processes were designed for a slower pace of change, and annual or milestone-based reviews made sense when systems were relatively static. That isn’t the case in a multi-cloud environment, where configurations change daily and new services are spun up continuously. The issue isn’t the Risk Management Framework itself. It’s the absence of modular ATO processes, reusable control implementation, and automated evidence collection that support ongoing authorization rather than periodic reassessment.
Limited and inconsistent visibility.
When CloudOps, security, and compliance data lives in separate systems managed by separate teams, no one has a complete picture. CloudOps teams may know what’s running but not whether it’s compliant. Security teams may know the policy requirements but not the current state of deployed resources. Compliance and ATO teams may be working from documentation that’s already out of date by the time it’s reviewed. This fragmentation also makes it harder to consistently access and deploy tools across environments, further slowing teams and limiting the ability to take advantage of innovation available within cloud service provider marketplaces.
Governance as a bottleneck.
When risk data is fragmented, routine decisions require reconciliation across multiple stakeholders. Approvals that should be straightforward become extended coordination exercises. Governance devolves into an outer checkpoint instead of an integrated function, slowing deployment cycles, and pushing teams toward work-arounds that introduce new risk.
The Challenges Are Real but Not Inevitable
Click image to enlarge, ESC to close.
×
It’s important to acknowledge that the siloed model evolved naturally from organizational structures that predated cloud adoption. CloudOps, security, and compliance were separate disciplines long before multi-cloud was a reality, and the processes built around them reflected a different era of IT.
But the operating environment has changed, and the model needs to change with it.
There is a better approach that treats CloudOps, security and compliance not as three separate worlds but as an integrated system of systems. Instead of building a service, securing it, and auditing it in sequence, agencies can align these functions so they operate together with the client mission experience at the center.
In this integrated model, security is built into the design process from the start; authorization is continuous rather than periodic; and operations, compliance, and governance share visibility and work from the same data.
The path from siloed operations to this integrated, mission-centered model is practical, it’s achievable, and it’s already underway in agencies across the federal and state landscape.
In our next post, we’ll walk through the practical steps agencies are taking to make that shift and show what the integrated model looks like in practice.
Download the Infographic for a quick, visual summary.
Frequently Asked Questions
Multi-Cloud Operations, Security, and Compliance
Explore common questions about siloed cloud operations, continuous authorization, and how agencies can align CloudOps, security, and compliance across multi-cloud environments.
Understanding the Problem
What's the difference between CloudOps, security, and compliance teams, and why does it matter if they're separate?
CloudOps teams build and manage cloud infrastructure and services. Security teams implement and monitor controls to protect those services. Compliance and ATO teams assess whether controls meet policy requirements and formally authorize systems to operate. When these teams work independently rather than as an integrated unit, agencies face duplicated effort, delayed decisions, late-stage rework, and governance bottlenecks that slow mission delivery.
How do I know if my agency has a siloed operations problem?
Common indicators include security reviews happening after deployment decisions are made, ATO processes that take months to complete, compliance documentation that is outdated by the time it is reviewed, routine approvals requiring extensive coordination across multiple teams, and limited visibility into whether running systems are actually compliant with current policies.
We're already managing multiple clouds successfully. Why should we worry about this now?
Managing multiple clouds and operating them efficiently are different challenges. While agencies can make multi-cloud work with existing processes, the hidden costs compound over time through delayed ATOs, security findings discovered late in the lifecycle, duplicated monitoring and documentation efforts, and governance structures that create bottlenecks rather than enable agility.
The Multi-Cloud Challenge
Why does multi-cloud specifically make this problem worse?
In a single-cloud environment, complexity is manageable because teams learn one set of controls, tools, and processes. Multi-cloud multiplies that complexity because each provider brings its own control models, compliance requirements, operational tooling, and governance processes. Each new cloud expands the attack surface and requires updates to security implementations, ATO packages, and monitoring strategies. When teams operate in silos, coordinating these changes becomes exponentially harder.
Our ATO process works fine for our current systems. Why does it need to change for multi-cloud?
Traditional ATO processes were designed for systems that changed slowly, where annual or milestone-based reviews made sense. Multi-cloud environments change continuously. Configurations update daily, new services spin up constantly, and security postures shift in real time. The Risk Management Framework itself remains valid, but agencies need modular ATO processes, reusable control implementations, and automated evidence collection to support ongoing authorization rather than periodic reassessment.
The Integrated Approach
What does "continuous authorization" actually mean in practice?
Continuous authorization means moving from periodic compliance assessments to ongoing verification of security posture. Instead of documenting controls once a year and hoping nothing changes, agencies continuously collect evidence that controls remain effective, automatically monitor for drift from approved configurations, and maintain real-time visibility into compliance status. This approach enables faster response to changes while maintaining or improving security assurance.
Do we need to reorganize our team structure to implement an integrated model?
Not necessarily. Integration is less about org charts and more about shared visibility, aligned processes, and collaborative workflows. Agencies can maintain separate CloudOps, security, and compliance functions while establishing shared data sources, integrated tooling, joint planning processes, and governance structures that enable rapid decision-making rather than creating bottlenecks.
What does it cost to stay siloed versus moving to an integrated model?
The cost of remaining siloed includes delayed ATO decisions that postpone mission capability delivery, duplicated effort across teams maintaining separate documentation and monitoring, rework triggered when security findings surface late in deployment, and opportunity costs when governance bottlenecks slow innovation. While transitioning to an integrated model requires upfront investment in process redesign and tooling, agencies typically see faster ATO timelines, reduced rework, and improved security posture that offset those costs.
Getting Started
Where should our agency start if we want to move toward this integrated model?
Start by establishing shared visibility across CloudOps, security, and compliance teams into the current state of cloud resources and their compliance posture. Next, identify high-friction points in your current processes, where delays occur, where rework happens, and where teams work from different versions of truth. Then pilot an integrated approach on a single cloud service or application, bringing teams together from the design phase through authorization. Use lessons learned to scale the model across your multi-cloud environment.
How does this integrated approach align with FedRAMP and other federal compliance frameworks?
The integrated approach strengthens compliance with federal frameworks by making security and compliance considerations part of design and operations from the start rather than afterthoughts. FedRAMP and other frameworks define what controls must be implemented and assessed. The integrated model defines how agencies implement those controls efficiently across multiple clouds while maintaining continuous visibility and authorization. Agencies can maintain full framework compliance while significantly improving speed, consistency, and operational efficiency.
What's coming in your next post?
Our next post will outline practical steps agencies can take to move from siloed CloudOps, security and compliance functions toward a more integrated operating model. It will cover service-centric organizational design, shared training and terminology, embedding security and compliance into daily operations, applying consistent security baselines across cloud providers, and making technical decisions that reduce long-term operational and compliance burden. It will also explore how this convergence helps agencies scale multi-cloud environments more securely, efficiently, and with governance built in from the start.



